
Understanding Mobile App Development Costs in the UAE
Navigating mobile app development costs in the UAE is key for success. Uncover essential insights to budget wisely and make informed decisions.
Move beyond ChatGPT wrappers. We build custom LLM integrations, RAG pipelines, and specialized machine learning models that actually solve complex business problems.

A global sourcing partner that manages complex supply chains and end-to-end logistics.

An established Oil & Gas engineering and construction firm in Turkmenistan.

A massive FMCG bulk retailer that relies on robust technical solutions to run high-volume operations.

A specialized financial services firm focused on Revenue Cycle Management.
Your team spends hours copying data from one system to another. We build practical AI layers that automate these tedious tasks so your staff can focus on high-value work.
You have years of historical data but no way to learn from it. We help you clean that data and build targeted predictive models that actually influence business decisions.
Hiring linearly to handle repetitive customer questions destroys profit margins. We build custom LLM-powered bots trained exclusively on your internal docs to handle tier-1 support.
Everyone is selling 'game-changing AI'. We're engineers, not magicians. We help you cut through the noise to find high-ROI use cases where machine learning actually makes financial sense.
If a simple SQL script solves your problem better than a $50k machine learning model, we will tell you. We don't build AI just for the sake of utilizing AI.
We aren't tied to OpenAI or Google. We benchmark models objectively and recommend the right tool for your privacy needs and budget—whether that's GPT-4, Claude, or a self-hosted Llama instance.
We don't spend six months in 'research phases'. We build functional proof-of-concepts in days using existing foundation models to validate ROI before you commit serious budget.
An AI model is useless if your team can't use it. We are full-stack engineers who seamlessly wire these models into your existing web, mobile, and internal tools.

Integrate Large Language Models (LLMs) like GPT-4 or Claude into your applications to automate content generation, summarization, and complex reasoning tasks.
Develop bespoke predictive models tailored to your specific datasets for forecasting, anomaly detection, and advanced data classification.
Build intelligent, context-aware chatbots and virtual assistants that understand natural language and execute complex workflows on behalf of users.
Implement image and video analysis systems for automated quality control, facial recognition, document processing (OCR), and visual search.
We help you identify the highest-impact areas for AI adoption within your business and create a roadmap for implementation and team upskilling.
Tailored digital solutions for high-impact sectors.

We analyze your business processes to find where AI can deliver the highest ROI and solve critical inefficiencies.
We evaluate the quality, quantity, and structure of your existing data to ensure it is ready for machine learning applications.
We quickly build a Proof of Concept to validate feasibility, test model accuracy, and ensure the solution aligns with business goals.
We fine-tune the algorithms and seamlessly connect the AI engine into your existing software infrastructure via secure APIs.
Post-deployment, we continuously monitor model performance, preventing data drift and retraining the AI to maintain high accuracy over time.
We provide comprehensive software development services including custom software development, AI solutions, cloud migration, cybersecurity, web and mobile app development, and IT consulting. Our team specializes in building scalable, secure solutions tailored to your business needs.
Software development costs vary based on project complexity, features, and timeline. Simple applications start around $15,000-$50,000, while enterprise solutions range from $100,000+. We provide transparent pricing and detailed quotes after understanding your requirements. Book a free consultation to discuss your project.
Development timelines depend on project scope. A basic application takes 2-3 months, mid-complexity projects require 4-6 months, and enterprise systems may take 6-12 months. We follow agile methodology with regular updates, allowing you to see progress every 2 weeks. We provide accurate timelines during the discovery phase.
Custom software is built specifically for your business, offering perfect alignment with workflows, scalability, and competitive advantages. Off-the-shelf solutions are generic products with limited customization. While off-the-shelf is cheaper initially, custom software provides better ROI long-term by eliminating workarounds and licensing fees.
Yes! We offer comprehensive post-launch support including bug fixes, performance monitoring, security updates, feature enhancements, and 24/7 technical support. Our maintenance plans ensure your software stays secure, performs optimally, and evolves with your business needs. Most clients opt for our monthly or annual support packages.
Tell us what you're building. No project managers, just engineers reviewing your tech stack.
We'll get back to you within a day with technical feedback and actionable next steps.
Your intellectual property is sacred. We sign an NDA before you share a single line of code.
Once we agree on the scope and terms, our team starts writing production code within 48 hours.
Whether you need a full engineering team to build from scratch or an expert audit to fix scaling issues, we're ready to dive in. Drop us a message—you'll speak directly with a senior engineer, not a sales rep.
Explore expert insights on AI/ML, Cloud Computing, DevOps, Cybersecurity, Blockchain, and other cutting-edge technologies shaping the future of business.

Navigating mobile app development costs in the UAE is key for success. Uncover essential insights to budget wisely and make informed decisions.
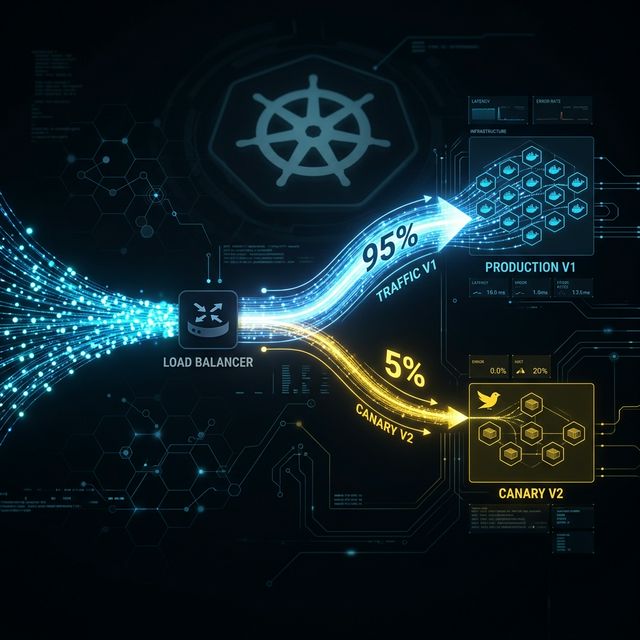
Canary deployment is one of the few strategies that genuinely changes your relationship with production. Learn how it works, what to monitor, the rollback mechanics, and the architecture prerequisites most tutorials skip.

How the India–EU Free Trade Agreement is unlocking new opportunities for IT talent and businesses